WHAT WE DO
Abricto Security is redefining offensive security and the value it brings to our customers. Discovering exploitable security flaws, accurately defining contextual risk, providing specific and actionable remediation guidance, and validating remediation are all critical components of our approach. Our assessments and service offerings are customized to deliver these components to our clients in a way that best fits their needs.

PARTNERSHIP AND COMMITMENT DRIVE DIFFERENTIATED VALUE
We are not just another pen testing vendor. Our consulting and internal development teams enable Abricto Security to build highly customized solutions for our clients, such as AppSec as a Service and Aardwolf, and to deliver integrated solutions and custom features by request. Clients that are committed to partnering with us can always count on Abricto to deliver.

OUR SERVICES & ASSESSMENTS
Abricto Security offers a wide array of specialized assessments to measure and quantify the effectiveness of your organization’s security controls. These are great snapshots of current security posture. Services are on-going partnerships designed to iteratively improve security controls and practices.
LATEST BLOGS
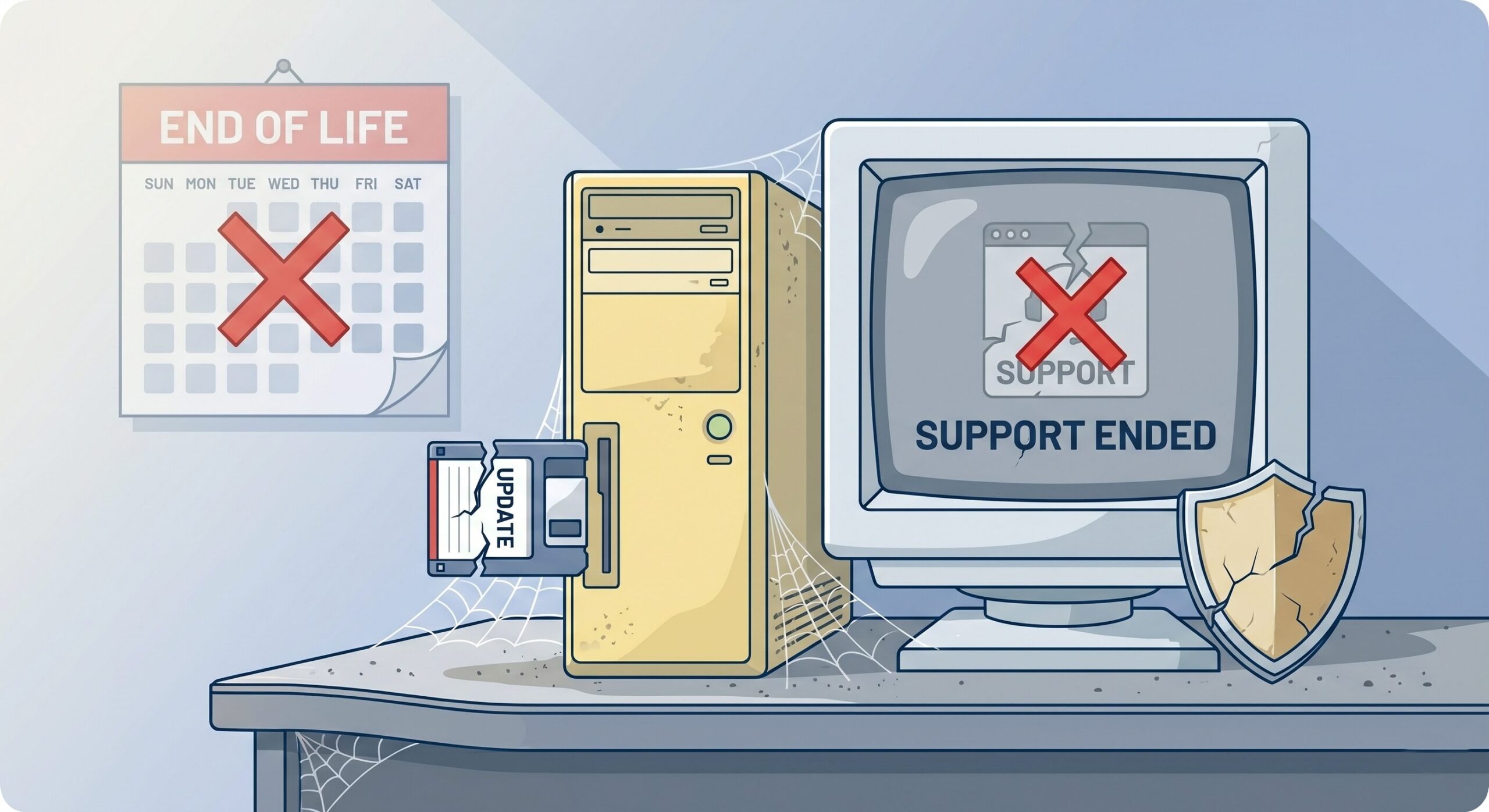
Unsupported. Unpatched. Why does the distinction matter in software?
Introduction At my previous employer, I was responsible for putting together data slides for the Cybersecurity steering committee presentation. I would end up with a lot of: Incomplete data Inconsistent data Data that wasn't telling ...
Active Directory Artifacts – Group Policy Preferences
One of the first things I check during an internal is GPP credentials. If you know the environment is older, this is a quick way to potentially obtain valid credentials. They are usually configured by ...
Attacks You Should Know About: IDOR
Welcome back to the "Attacks You Should Know About" series! It's been a while, but we're coming back with one of the most prevalent vulnerabilities in web applications: Insecure Direct Object References, more commonly known ...