Our team researches and documents bleeding-edge security concepts and hacking techniques.
This blog explores these topics and more to keep you informed.
Attacks You Should Know About: IDOR
Welcome back to the "Attacks You Should Know About" series! It's been a while, but we're coming back with one of the most prevalent vulnerabilities in web applications: Insecure Direct Object References, more commonly known ...
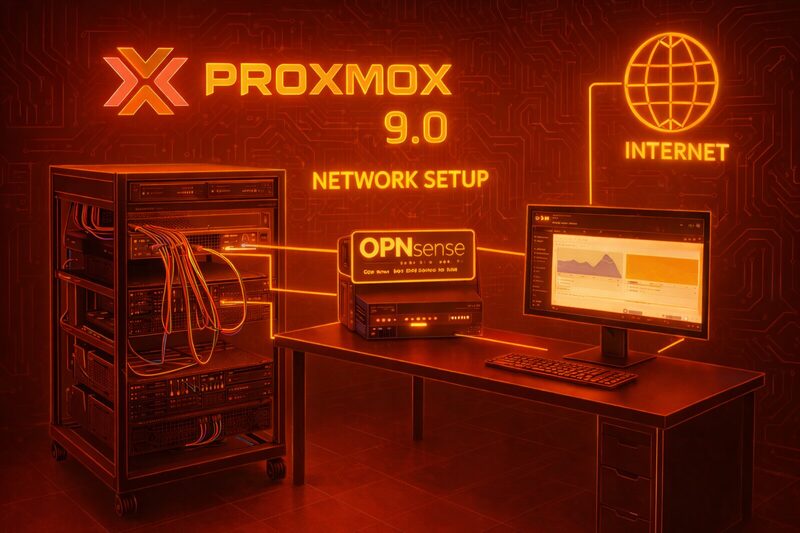
HomeLab Series: Network Architecture – Bridges & OPNsense
Configure Proxmox network bridges and deploy OPNsense as an open source edge firewall - fully scripted, zero subscriptions. Abricto Security HomeLab Series.
Wireless Pentesting: Wireless Adapters
At its core, wireless pentesting has not changed much over the past few decades, but wireless adapter technology has advanced significantly. To conduct an effective wireless pentest, you need an adapter that supports monitor ...
Blackboxing the Kube: Why Your Cluster is Only as Strong as Its Weakest Link (or Lack Thereof)
Congratulations. You’ve successfully containerized your legacy monolith, slapped it into a Kubernetes cluster, and now you’re telling your stakeholders that you’re “cloud-native.” It’s a beautiful sentiment, really. You’ve traded the headache ...
My Digital Monsters
If you've spent any time in the physical hacking tool space, you're probably familiar with the usual suspects: WiFi Pineapples for deauthentication attacks, USB Rubber Duckies for payload delivery, and badge cloners for RFID shenanigans. ...
HomeLab Series: Proxmox on Refurbished Servers
Why and What Setting up a homelab can feel overwhelming at first. With an abundance of guides, opinions, and technical information available, taking the initial step may seem challenging. However, the long-term benefits far ...
Building Your Own Homelab Testing Environment
I do a lot of tool building and research in the container space for Windows. This often requires something called nested virtualization. What is Nested Virtualization? In simple terms, nested virtualization is the ability ...
OSINT: From Basic Tools to Advanced Techniques
What exactly is OSINT? Broadly speaking, OSINT—or Open-Source Intelligence—refers to the gathering, evaluation, and analysis of publicly available information to answer a specific question. This information can come from various sources, including public records, news ...
Understanding the Difference Between a Compiler and an Interpreter
When you write a program in a high-level language like Python or C++, you are using something that makes sense to us as humans, but not to your computer. It's similar to speaking a ...