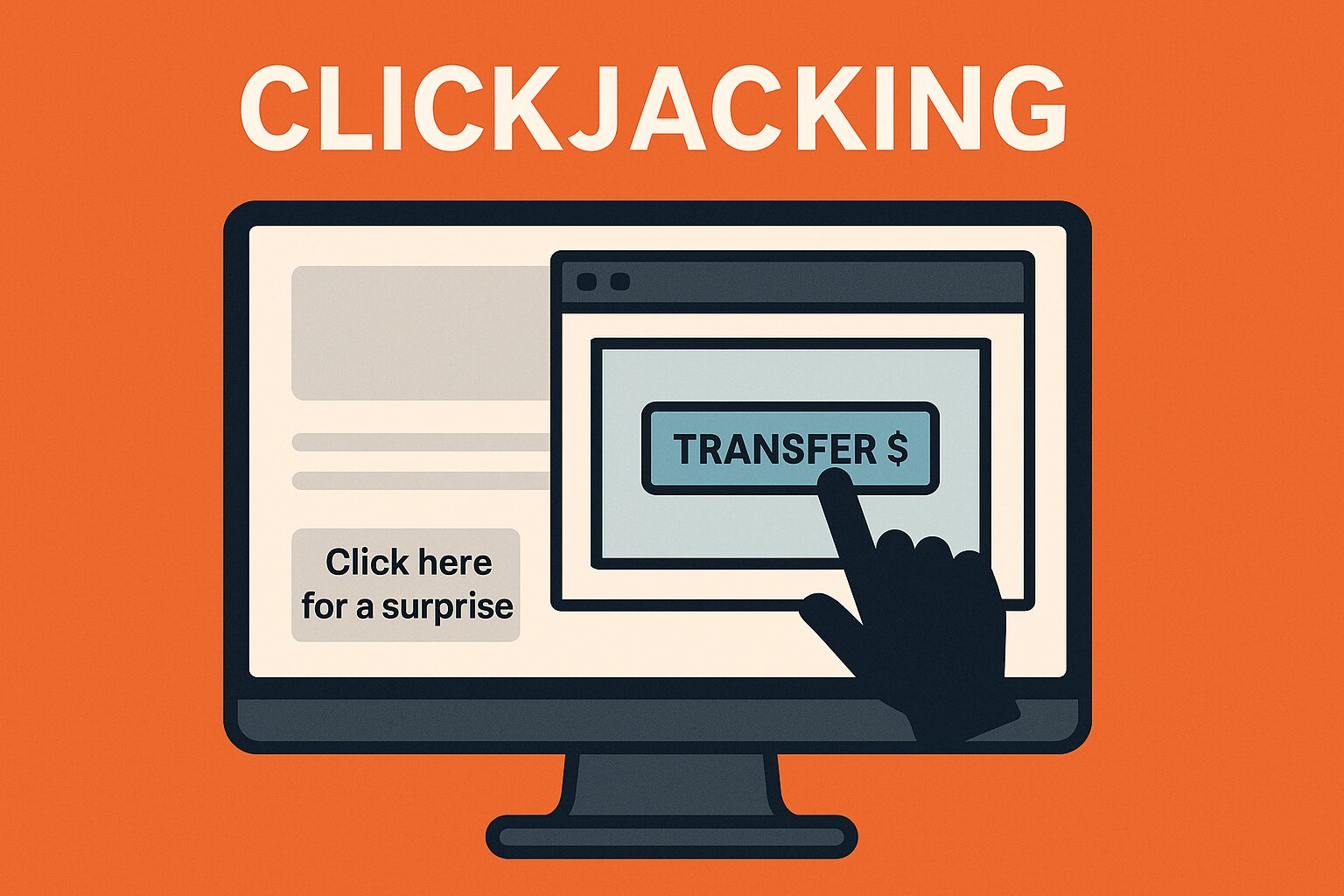
Attacks You Should Know About: Cross-Origin Resource Sharing
Welcome to the second installment of our "Attacks You Should Know About" series! This blog provides valuable insights for both novice and experienced cybersecurity professionals on common attacks and vulnerabilities. Today, we examine cross-origin resource ...