Introduction
Have you ever wondered how the top Software as a Service (SaaS) platforms keep their data safe? This article will explore the core concepts of securing SaaS applications. It’s packed with essential tips and strategies for building a solid security foundation, from keeping data encrypted to ensuring only the right people can access it. By the end, you’ll know exactly what it takes to secure your application..
Core Principles of SaaS Security

Security is indispensable for Software as a Service (SaaS) platforms as your app will hold a wealth of sensitive information like user data and payment information, making it imperative to keep this data safe from unauthorized access. Below are some of the key security principles that you should consider integrating into your platform to effectively protect users’ data.
Encryption Your Sensitive Data
Encrypting data in SaaS applications demands more than a one-size-fits-all approach; it requires a nuanced strategy. AES (Advanced Encryption Standard) with 256-bit keys is recommended for encrypting data at rest, as it provides a high level of security against brute force attacks.
For data in transit, TLS 1.3 protocol should be the standard, ensuring that data moving between the server and clients is encrypted with the most current and secure methods available. Implementing these technologies not only safeguards sensitive information from unauthorized access but also significantly enhances the overall security posture of your SaaS platform.
Utilize Modern Identity and Access Management:
Implementing a sophisticated access control system involves integrating modern Identity and Access Management (IAM) solutions that support multi-factor authentication (MFA) and role-based access control (RBAC).
MFA adds an additional layer of security by requiring users to verify their identity through two or more validation methods before accessing the application.
RBAC allows administrators to grant access rights based on the user’s role within the organization, ensuring that individuals can only access the information necessary for their job functions.
Utilizing IAM solutions that offer these features can drastically reduce the risk of unauthorized access and potential data breaches.
Conduct Regular Audits and Compliance Checks
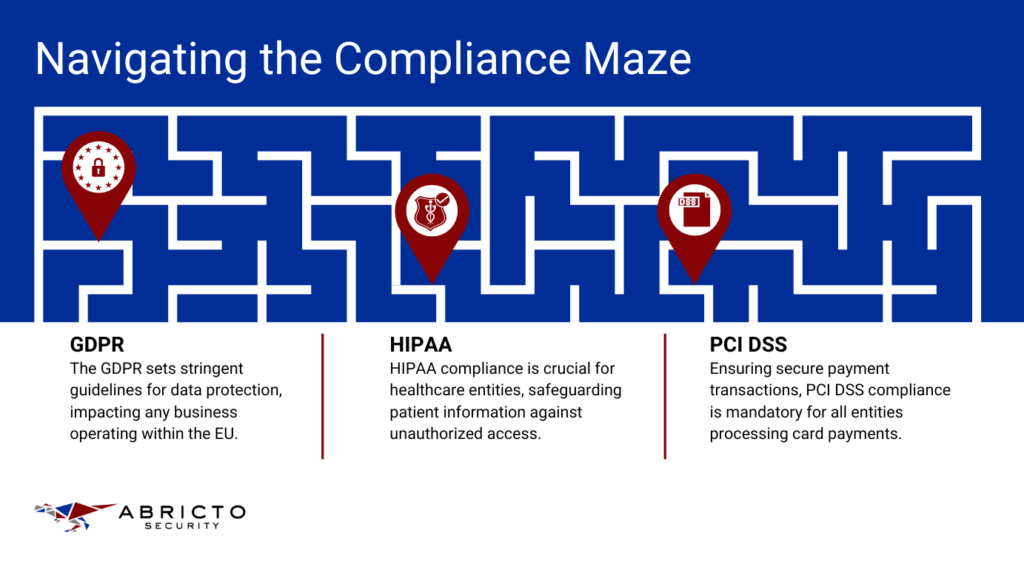
To stay aligned with legal and regulatory standards, SaaS platforms must adopt a proactive approach by conducting regular security audits and adhering to compliance regulations. Tools like automated compliance monitoring can streamline this process by continuously scanning for deviations from standards such as GDPR, PCI or HIPAA.
These tools can provide real-time alerts on non-compliance issues, allowing for immediate remediation. Regular security audits should be conducted using automated vulnerability scanners and manual penetration testing to identify and mitigate potential security vulnerabilities. Adopting these practices demonstrates a commitment to data security and privacy, fostering trust with users.
Threat Detection and Management
For guarding against threats, early detection and effective management of threats are crucial. Implementing a Security Information and Event Management (SIEM) system provides an integrated platform for real-time analysis of security alerts generated by applications and network hardware. Coupled with advanced threat intelligence services, SIEM systems can help in identifying emerging threats and vulnerabilities.
In addition, having an Incident Response Plan (IRP) in place ensures that your team is prepared to quickly and efficiently address security incidents. The IRP should outline specific procedures for containment, eradication, and recovery, along with clear communication strategies for internal and external stakeholders.
Designing Secure SaaS Architectures
Creating a secure foundation for SaaS applications begins with thoughtful design and architecture. By integrating security measures from the ground up, companies can protect their services against evolving threats.
Secure Software Development with DevSecOps
Integrating security into the software development lifecycle is essential. This means security considerations influence every stage of development; from initial design to deployment and maintenance. By adopting a DevSecOps approach, teams prioritize security, perform regular security testing, and automate security processes where possible, leading to more secure outcomes.
Key Architectural Considerations for Maintaining Security
When designing the architecture of a SaaS application, it’s important to plan for data segregation, encryption, and secure access protocols. Ensuring data is encrypted and appropriately segmented to prevent unauthorized access is key. Additionally, designing with privacy in mind means implementing features that allow for data anonymization and secure data deletion practices.
Utilizing Cloud-Native Security Features Effectively
Cloud platforms offer a range of built-in security features designed to protect applications and data. These include identity and access management tools, encryption services, and threat detection capabilities. Leveraging these features can provide a strong security posture, but it’s important to configure them correctly to effectively identify potential vulnerabilities.
Secure Software Development with DevSecOps
The DevSecOps approach embeds security principles from the initial design phase through to deployment and beyond, ensuring that security is not an afterthought, but a fundamental component of development.
This involves:
- Continuous Integration/Continuous Deployment (CI/CD) Pipelines: Implement CI/CD pipelines that incorporate security checks, such as static application security testing (SAST) and dynamic application security testing (DAST), to identify vulnerabilities early.
- Automated Security Testing: Leverage automated tools to scan code for security flaws in real-time, significantly reducing the time to detect and rectify issues.
- Security Training for Developers: Equip your development team with the knowledge to identify and mitigate security risks, emphasizing the importance of secure coding practices.
Key Architectural Considerations for SaaS Security
Designing the architecture of a SaaS application with security in mind requires meticulous planning and execution.
Key considerations include:
- Data Segregation: Ensure that customer data is stored and processed in isolation from other tenants, using database schemas or separate database instances to prevent data leaks between users.
- End-to-End Encryption: Implement end-to-end encryption for data in transit and at rest, utilizing protocols such as TLS for data in transit and AES for data at rest, to protect sensitive information from interception and unauthorized access.
- Privacy-Enhancing Technologies: Design your systems to incorporate privacy-enhancing technologies (PETs) that enable data anonymization and secure deletion, ensuring that users’ privacy is maintained and regulatory compliance is met.
Leveraging Cloud-Native Security Features for SaaS Applications
Cloud-native security features provide a foundational layer of protection for SaaS applications.
To effectively utilize these features:
- Identity and Access Management (IAM): Use cloud IAM services to control who can access your cloud resources and how they can interact with them. Implement least privilege access policies and use MFA to enhance security.
- Encryption Services: Take advantage of the cloud provider’s encryption services to secure data at rest and in transit, ensuring that encryption keys are managed securely.
- Threat Detection: Utilize cloud-native threat detection services to monitor for suspicious activity and potential security threats. These services can offer real-time alerts, enabling swift action to mitigate risks.
By embracing these detailed strategies and technologies, SaaS founders and security professionals can fortify their applications against a wide array of security challenges, ensuring the protection of their data and the trust of their users.
Implementing Essential Security Tools and Practices

Employing the right security tools and practices is necessary to safeguard data and ensure service continuity. This means integrating a suite of security solutions, such as firewalls, intrusion detection systems, and encryption protocols, to create a layered defense strategy.
Firewall
Firewalls act as the first line of defense in securing SaaS applications by monitoring and controlling incoming and outgoing network traffic based on predetermined security rules.
For comprehensive protection, employ both network firewalls to shield the perimeter and web application firewalls (WAFs) to specifically protect the application layer from web-based attacks.
Network firewalls can be configured to restrict traffic to and from certain locations, while WAFs are crucial for mitigating common web vulnerabilities such as SQL injection and cross-site scripting (XSS). Regularly updating firewall rules and configurations to adapt to new threats is important for maintaining a strong defense.
Regular Updates and Patch Management
Keeping your software and systems updated is a cornerstone of good cybersecurity hygiene.
An effective patch management strategy involves:
- Automated Monitoring: Use tools that automatically monitor for software updates and vulnerabilities relevant to your technology stack.
- Prioritization: Assess the criticality of each update or patch to prioritize deployment, focusing first on those that address high-risk vulnerabilities.
- Testing: Before widespread deployment, test patches in a controlled environment to ensure they do not introduce new issues.
- Documentation: Keep detailed records of patches and updates applied to facilitate audits and troubleshooting.
This approach not only closes potential security gaps but also ensures that your application remains compatible with the latest security standards and technologies.
Intrusion Detection Systems
Intrusion Detection Systems (IDS) are essential for identifying potentially malicious activities within your network.
There are two main types:
- Network-based IDS (NIDS): Monitors network traffic for suspicious activity and alerts administrators to potential threats.
- Host-based IDS (HIDS): Installed on individual devices to monitor inbound and outbound signals and system configurations for signs of intrusion.
For SaaS platforms, integrating both NIDS and HIDS offers a more complete view of potential security threats, both at the network and host levels. Implementing automated response mechanisms, such as temporarily blocking suspicious IP addresses, can further enhance security.
Incident Response Plan
Despite all preventive measures, security incidents can still occur.
An effective Incident Response Plan (IRP) includes:
- Preparation: Educate and train your team on their roles during an incident. Conduct regular drills to ensure readiness.
- Detection and Analysis: Implement systems for early detection of incidents. Once detected, quickly analyze the scope and impact.
- Containment, Eradication, and Recovery: Contain the incident to prevent further damage, eradicate the root cause, and recover affected systems to normal operation.
- Post-Incident Analysis: After an incident, review and analyze what happened, why, and how it was handled. Update your IRP based on these insights to strengthen your defenses against future incidents.
Clear communication is vital throughout this process, both internally and with affected stakeholders. Providing transparent and timely information helps preserve trust and demonstrates your commitment to security and privacy.
The Role of Compliance in SaaS Security
In the world of SaaS, compliance helps maintain trust with users while ensuring that data is handled securely. Key regulations such as the EU’s General Data Protection Regulation (GDPR) and the Health Insurance Portability and Accountability Act (HIPAA) in the US set stringent data privacy and security requirements.
These standards dictate how data should be collected, processed, stored, and protected, guiding SaaS providers in implementing necessary security measures to protect user information and avoid substantial fines.
Adhering to compliance standards helps SaaS companies establish a solid security framework. By aligning with these regulations, SaaS companies can identify and mitigate risks more effectively, ensuring that they meet legal obligations and strengthen their overall security posture.
Compliance drives the implementation of stringent data protection policies, regular security assessments, and continuous monitoring, laying the groundwork for a secure and trustworthy SaaS platform.
How ASaaS Can Secure Your SaaS Security
Keeping your SaaS application safe involves a lot of steps – like encrypting data, managing who gets access, and following regulations. It can get really complicated, especially if you’re not a security expert. That’s where engaging Application Security as a Service (ASaaS) comes in handy.
Think of ASaaS as your go-to security team that has all the tools and know-how to protect your app from threats. By leveraging ASaaS, you’re bringing on experts who can handle the tough security stuff, so you can focus on growing your business. If making sure your app is secure sounds overwhelming, it’s time to get some help.
Book a call with us today, and let’s talk about how we can help keep your SaaS app safe.
